Data breaches in hospitality cost operators an average of $4.45 million per incident, according to IBM’s 2024 Cost of a Data Breach Report. Guest information-credit cards, personal details, booking histories-makes hotels prime targets for cybercriminals.
At Clouddle, we’ve seen firsthand how hospitality data security best practices separate properties that thrive from those that struggle with compliance and reputation damage. This guide walks you through the concrete steps your team needs to protect guest data and build genuine security resilience.
Why Data Security Matters in Hospitality
Guest Trust Collapses After a Breach
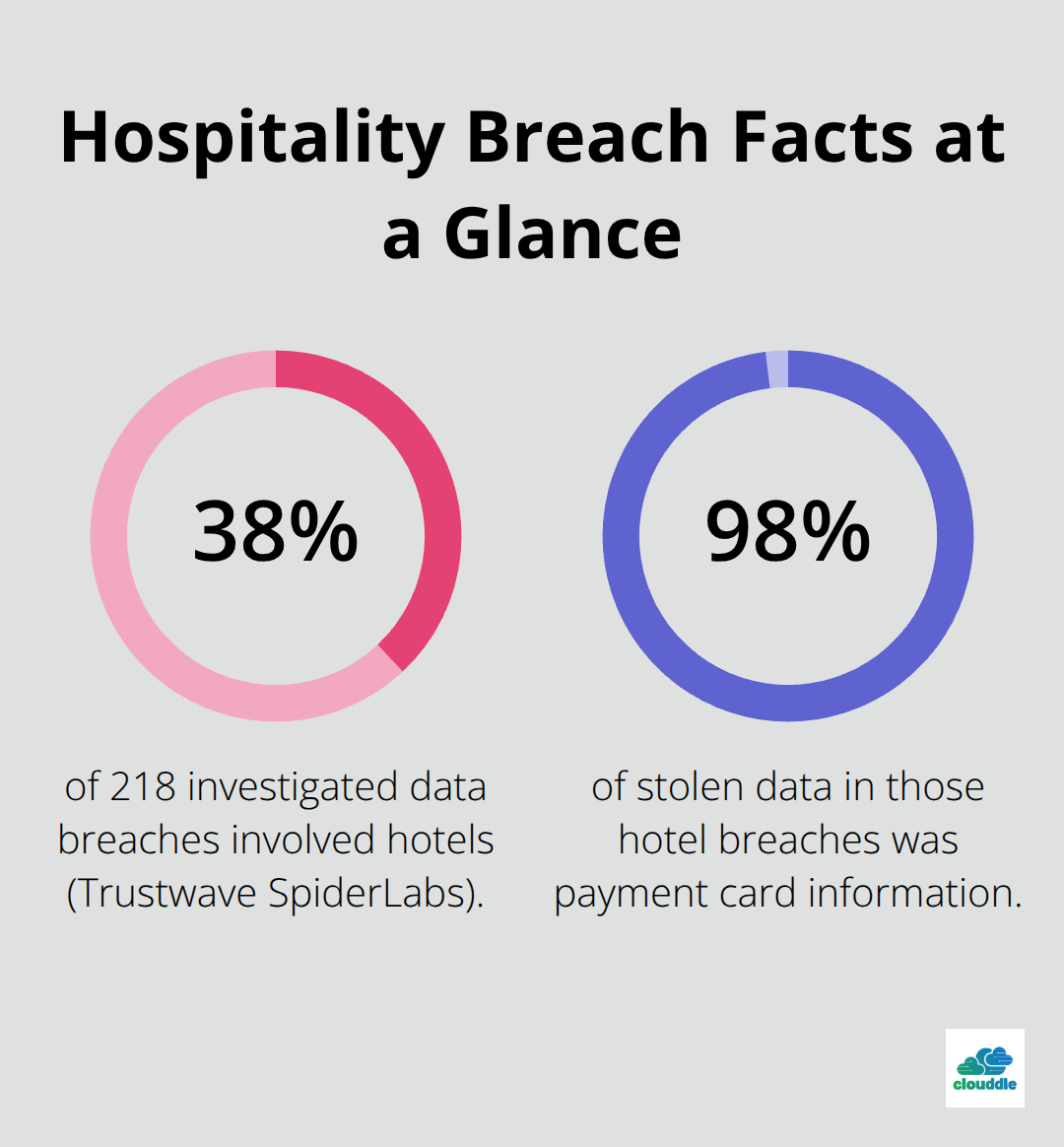
Guest trust evaporates the moment a breach becomes public. Marriott’s Starwood breach exposed up to 339 million guest records, resulting in a £18.4 million fine from the UK Information Commissioner’s Office. The breach began in 2014 and remained undetected until 2018-guests had no idea their passport numbers, payment information, and travel plans were exposed for years. When guests learn their data was compromised, they stop booking with you. They switch to competitors. They leave negative reviews that damage your online reputation for months. The Hilton breach of 2014–2015 triggered regulatory scrutiny and a $700,000 penalty for delayed notification and inadequate security measures. These incidents are not isolated. Trustwave SpiderLabs found that 38 percent of 218 data breach investigations across 24 countries involved hotels, with 98 percent of stolen data being payment card information.
The Data You Collect Attracts Cybercriminals
Your property collects names, addresses, phone numbers, credit card details, passport numbers, and travel plans-exactly what cybercriminals want. IBM’s 2024 Cost of a Data Breach Report shows hospitality data breaches cost an average of $4.88 million per incident. That figure includes incident response, regulatory fines, guest notification, credit monitoring services, legal fees, and reputational recovery. For smaller independent properties, a single breach can mean closure. The financial exposure is staggering because attackers target hospitality operators specifically for the volume and sensitivity of guest information they hold.
Regulatory Penalties Reach Millions
Regulatory penalties add another layer of risk that many operators underestimate. GDPR penalties reach up to €20 million or 4 percent of worldwide annual revenue-whichever is higher. If your property processes guest data from European visitors, you must obtain explicit consent for marketing, honor guest rights to access and delete their data, and notify regulators of breaches within 72 hours. Spain’s Royal Decree 933/2021 requires traceability of personal data to cooperate with authorities while protecting guest privacy. In the United States, 17 states now have comprehensive privacy laws including the California Consumer Privacy Act and Connecticut’s Data Privacy Act, with enforcement actions increasing. The Otelier breach in 2024 exposed millions of guest records and 7.8 terabytes of data when attackers used stolen credentials to access Amazon S3 storage-a supply chain failure that demonstrates the vulnerability of third-party systems.
You Own the Liability, Not Your Vendors
You cannot outsource your security responsibility to third-party vendors. You own the guest relationship and the liability when data is compromised. Your property management system, booking engine, cloud storage, and loyalty platform all hold sensitive information. Each vendor represents a potential breach vector. Operators who treat security as a checkbox rather than an ongoing practice inevitably face costly incidents. Those who implement genuine security resilience-network segmentation, multi-factor authentication, regular audits, and continuous staff training-reduce their breach risk substantially and build guest confidence that translates to bookings and loyalty. The next section outlines the essential security measures your team needs to implement today.
How to Lock Down Your Property Network and Systems
The gap between properties that experience breaches and those that don’t comes down to implementation, not intention. Most operators know they need security measures, but they implement them halfway or skip them entirely because they seem complex. The sections below outline the concrete steps your team must take to protect guest data at every layer of your operation.
Separate Your Networks to Protect Payment Data
Network segmentation separates your guest Wi-Fi from your administrative systems where payment processing and guest data live. This is not optional if you process credit cards. The PCI Security Standards Council requires physical or logical separation of cardholder data environments from guest-facing networks. Start by identifying which devices and systems handle payment data, which serve guests, and which manage back-office operations. Then physically separate them using firewalls that block traffic between segments unless explicitly permitted.
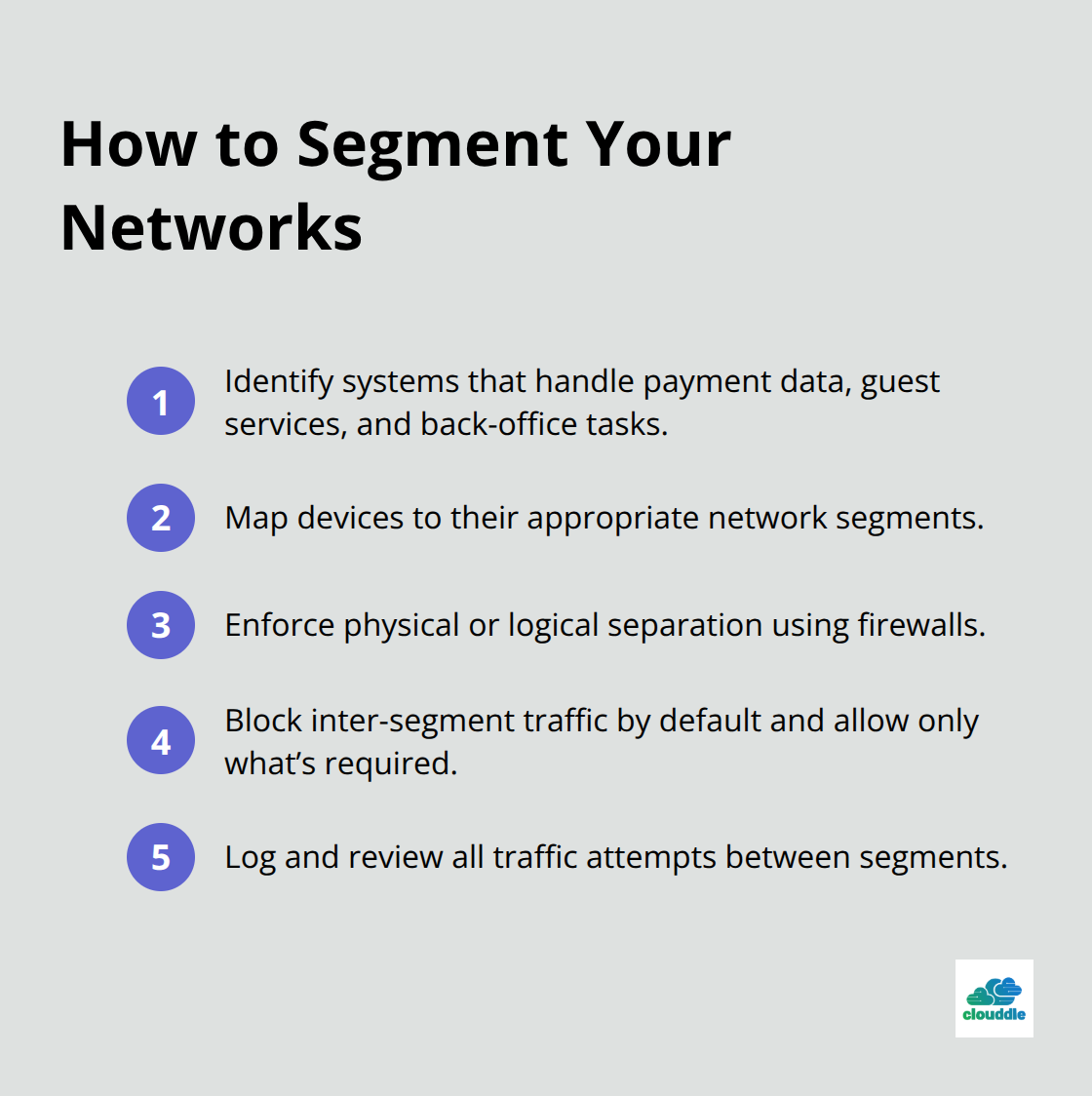
A property that processes 200 bookings monthly through a single unsegmented network exposes every guest’s payment information to anyone on the guest Wi-Fi. The same property with proper segmentation limits an attacker’s reach to guest browsing data, not credit cards or passport scans. Your firewall should log all traffic attempts between segments so you have evidence of what was blocked and what succeeded.
Require Multi-Factor Authentication for Staff Access
Multi-factor authentication adds a second verification step when staff log into systems that hold guest data. A staff member enters their password, then receives a code on their phone or authenticator app before access is granted. This stops attackers who steal passwords from logging in remotely. The Otelier breach in 2024 began when attackers used stolen credentials to access cloud storage, yet proper MFA would have prevented that access.
Enforce MFA on your property management system, email accounts, and any cloud services where guest data lives. Do not allow staff to use shared login credentials or personal email addresses for business systems. Rotate passwords every three months and require unique, complex passwords that don’t reuse patterns from previous logins. These practices eliminate the most common attack vector: compromised employee credentials.
Conduct Quarterly Security Audits
Conduct regular security audits by either hiring an external firm or using your managed IT provider to scan for vulnerabilities in your systems quarterly. These audits identify outdated software versions, missing security patches, and misconfigurations that attackers exploit. After each audit, prioritize patching critical vulnerabilities within 30 days and medium-severity issues within 60 days. Keep patch records to demonstrate compliance during regulatory inspections.
Properties that audit quarterly catch vulnerabilities before attackers find them; those that skip audits discover breaches months or years later. An audit also reveals which third-party vendors (your PMS provider, booking engine, cloud storage service) have security gaps that put your guest data at risk. Use audit findings to hold vendors accountable and negotiate stronger data protection clauses in your contracts.
Your security posture improves measurably when you treat these three measures-network segmentation, multi-factor authentication, and regular audits-as non-negotiable operational standards rather than optional upgrades. The next section addresses how your team’s behavior and training directly impact whether these technical controls actually work in practice.
Your Team Is Your Biggest Security Vulnerability
Technical controls fail when staff ignore security protocols or fall for phishing attacks. Staff training and a dedicated cybersecurity champion measurably improve security posture across properties. This means your front desk, housekeeping, and back-office teams need specific, practical training that sticks-not generic annual compliance videos.
Enforce Strong Password Practices
Start with password management. Require staff to use unique, complex passwords for every business system and rotate them every three months without reusing previous patterns. Prohibit shared login credentials and personal email addresses for accessing guest data or payment systems. A single staff member sharing a password with a colleague creates two problems: you cannot trace who accessed sensitive data, and you lose the protection that multi-factor authentication provides.
Train Staff to Spot Phishing Attacks
Train staff to recognize phishing emails that impersonate guests, vendors, or management asking for passwords or guest information. The Otelier breach began with stolen credentials, likely obtained through phishing or credential reuse. Show staff real examples of suspicious emails and have them report anything unusual to a designated security contact. Conduct quarterly phishing simulations where you send fake malicious emails to staff and track who clicks suspicious links or enters credentials. Properties that run simulations quarterly catch 70 percent of risky behavior and see dramatic improvement in staff awareness within six months. Make reporting safe and reward staff who flag suspicious activity rather than punishing them for clicking a test email.

Document Data Handling Protocols
Establish written data handling protocols that define exactly how staff collect, store, and dispose of guest information. Specify that payment card details should never appear on paper or remain in unencrypted files. Guest passport scans should stay in a secure, access-restricted folder with automatic deletion after 30 days unless legal requirements demand longer retention. Assign one staff member responsibility for responding to guest requests to access or delete their data under GDPR and state privacy laws-do not let requests get lost in email chains. Centralize these requests through a single system to track compliance and prove you responded within required timelines.
Monitor Access Logs for Suspicious Activity
Implement access logging on all systems that hold guest data. Your property management system, booking engine, and cloud storage should record who accessed what data and when. Review access logs monthly for unusual patterns-such as a front desk clerk accessing guest passport scans after midnight or a staff member accessing payment data from multiple properties. Unusual access often signals compromised credentials or an insider threat. These practices (realistic staff training with measurable outcomes, explicit written protocols, and continuous access monitoring) transform your team from a liability into your strongest defense against data breaches.
Final Thoughts
Hospitality data security best practices rest on three pillars: technical controls, staff accountability, and continuous operational oversight. Network segmentation, multi-factor authentication, and quarterly security audits form your technical foundation, while staff training on password hygiene and phishing recognition ensures those controls function in the real world. Assign one staff member as your security champion to coordinate audits, manage vendor relationships, and track compliance with GDPR, state privacy laws, and PCI requirements. Conduct tabletop exercises annually where your team walks through breach scenarios and tests your incident response plan-these exercises expose gaps before a real breach occurs.
Start this month with a data audit to map where guest information flows through your systems and identify which vendors hold sensitive data. Prioritize network segmentation if you haven’t implemented it, enforce multi-factor authentication on all staff accounts accessing guest data, and schedule your first external security audit within 90 days. If your IT infrastructure feels outdated or you lack in-house expertise, a managed IT provider who understands hospitality security requirements can accelerate your progress significantly.
We at Clouddle provide managed IT, networking, and security services specifically designed for hospitality operators, with 24/7 support to keep your systems secure and compliant. Contact Clouddle to strengthen your security posture while your team focuses on guest experience. The operators who act now will outpace competitors who delay, building guest trust and avoiding the multimillion-dollar cost of a breach.



0 Comments