Hotels handle sensitive guest information and payment data every single day. A single security breach can expose thousands of records, trigger compliance violations, and damage your reputation for years.
At Clouddle, we’ve seen how hotel network security directly impacts both guest safety and your bottom line. This guide covers the threats you face, the vulnerabilities in your systems, and the practical steps to protect what matters most.
Why Hotel Network Security Matters
Cybersecurity ranks as the top concern for hotel executives, with 46% naming it their leading issue ahead of downtime and staffing challenges. This isn’t paranoia-it reflects real costs. The average hospitality data breach runs $3.4 million, and 31% of hospitality firms have already experienced one. Your network holds guest names, email addresses, credit card numbers, booking histories, and preferences that criminals actively target for identity theft and financial fraud.
Breaches Halt Operations and Drain Revenue
A breach stops your entire operation cold. When attackers hit your Property Management System or payment terminals, guests cannot check in, reservations vanish from your system, and online bookings halt. Revenue evaporates while you scramble to restore services, and regulatory fines pile on top of remediation costs. GDPR violations alone can cost up to 4% of your global annual turnover. Hotels that experience ransomware attacks often lose days of bookings and spend tens of thousands on recovery. The damage extends far beyond the immediate incident-guests who experience a breach rarely return, and negative word spreads fast online. One breach can tank your reputation for years and destroy your direct booking rates, which hospitality operators depend on for profitability.
Guest Trust Translates to Direct Bookings
Guests care deeply about data handling. According to Cisco’s 2022 research, 81% say how a company handles data reflects how it views its customers, and 76% won’t purchase from companies they don’t trust to manage their information. Yet 89% of people worry about privacy, and 82% are ready to switch brands to protect it.

When guests trust you with their data, they book directly instead of using third-party platforms, and they return. When they don’t trust you, they leave bad reviews and abandon you for competitors. Hotels that prioritize network security, encryption, access controls, and staff training signal to guests that their information is safe. This builds the loyalty that keeps rooms booked and rates high.
What Attackers Actually Target
Your network faces constant threats because it contains high-value targets. Attackers focus on payment systems (credit card data), the PMS (booking and guest information), and Wi-Fi networks (entry points to internal systems). They exploit weak passwords, unpatched software, and untrained staff who fall for phishing emails. A single compromised staff account can give attackers access to thousands of guest records. The hospitality industry’s digital transformation-with online bookings, mobile check-in, in-room IoT devices, and digital payments-expands your attack surface and increases exposure of guest data. Understanding these specific threats helps you build defenses that actually work.
The next section covers the most common attacks hotels face and why they succeed so often.
Common Security Threats Facing Hotels
Ransomware remains the most destructive attack hotels face. Attackers infiltrate your network through phishing emails sent to staff, then encrypt your Property Management System, payment terminals, and guest databases. You cannot access your own data until you pay the ransom, and even then, recovery takes days. Trustwave’s 2023 Hospitality Sector Threat Landscape found that 31% of hospitality firms experienced a breach, and 89% faced repeated attacks. Ransomware is relentless because it targets your most critical system-the PMS-which manages every booking, every guest record, and every payment. When your PMS goes down, your entire operation freezes.
Guests cannot check in, reservations disappear, and online booking channels go dark. One mid-size hotel paid $300,000 in ransom plus another $500,000 in recovery and lost revenue after a single attack. The cost climbs because you need forensic experts, IT restoration specialists, and guest notification lawyers. Preventing ransomware requires three actions: block phishing emails at the gateway, patch your PMS and all connected systems weekly, and segment your network so that if one system is compromised, attackers cannot reach your payment systems or guest databases.
Wi-Fi Networks Expose Your Entire Operation
Guest Wi-Fi networks are where attackers gain their initial foothold. Most hotels use a single Wi-Fi network for guests and staff, which is catastrophic. An attacker connects as a guest, positions themselves on the same network as your PMS, and uses packet sniffing tools to intercept unencrypted traffic or launch man-in-the-middle attacks. They capture credit card data, staff credentials, or booking information passing across the network. Worse, they use your guest network as a staging ground to attack your internal network.
Network segmentation stops this threat cold. Create a separate Wi-Fi network for guests with no access to internal systems, and restrict staff Wi-Fi to staff only with strong encryption and multi-factor authentication. Change the default password on your Wi-Fi router immediately-most hotels never do, leaving the router accessible to anyone who knows the default credentials. Update your Wi-Fi routers monthly and disable guest access to any internal services or device management interfaces. Monitor your network for unusual traffic patterns and bandwidth spikes that suggest someone is harvesting data or launching attacks from inside your network.
Payment Systems Face Constant Attacks
Payment card breaches expose your hotel to PCI DSS compliance violations, which carry fines up to $100,000 per incident. Attackers target point-of-sale terminals at your front desk, in-room payment systems, and mobile payment apps. They install skimming malware on terminals or intercept card data in transit if your systems use unencrypted connections. A breach means notifying every guest whose card was compromised, covering their fraud liability, paying forensic investigators, and facing regulatory audits.
Encryption forms your primary defense. Use TLS 1.2 or higher for all payment data in transit, and AES-256 encryption for data at rest. Implement tokenization so that payment terminals never store actual card numbers-they store tokens instead. Require multi-factor authentication for anyone accessing payment systems or guest financial data.
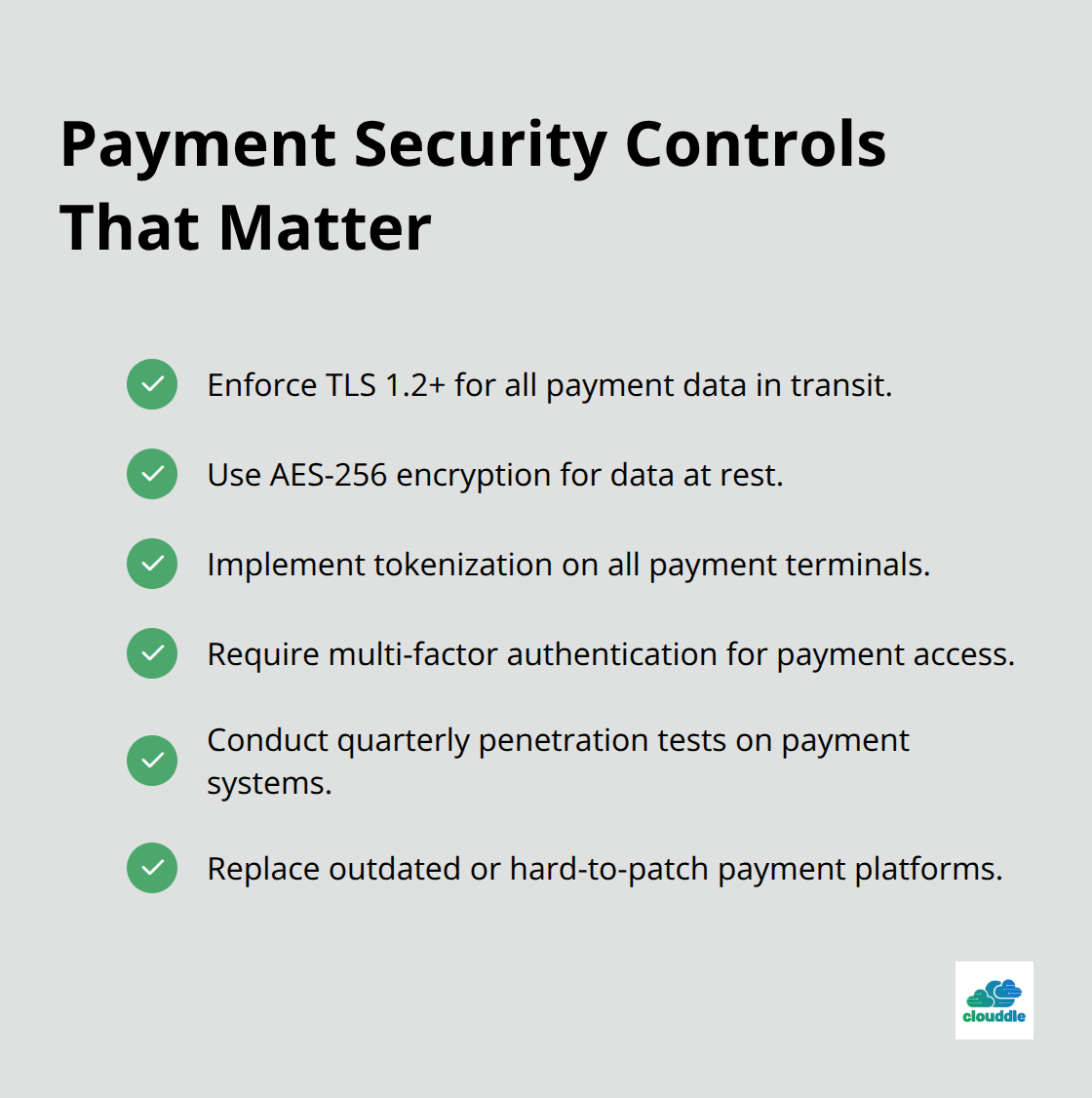
Conduct quarterly penetration tests on your payment infrastructure specifically to find weaknesses before attackers do. If your payment system is old or difficult to patch, replace it. The cost of a new payment system is trivial compared to a breach.
Human Error Remains Your Weakest Link
Staff members inadvertently open doors for attackers. Human error in hospitality cybersecurity is a persistent vulnerability that organizations must address through systematic training and awareness programs. A single staff member who clicks a phishing link, shares a password, or leaves a terminal unlocked can expose thousands of guest records. Attackers know this and target your team with convincing emails that appear to come from vendors, payment processors, or management.
Training transforms your staff into your strongest defense. Teach employees to verify identities by contacting known IT personnel directly, never share passwords, and report suspicious activity immediately. Run phishing simulations quarterly to identify which staff members need additional training. Enforce strong, unique passwords for every system and require multi-factor authentication on all critical systems (the PMS, payment terminals, email, and administrative accounts). Limit system access based on job role-front desk staff should not access financial records, and housekeeping should not access the PMS. These controls prevent attackers from exploiting a single compromised account to access your entire network.
Your network faces threats from multiple angles simultaneously. The next section covers how to build defenses that address all of these attack vectors at once.
How to Build Network Security That Actually Works
Segment Your Networks Into Separate Zones
Network security requires layers, not single solutions. Start with network segmentation, which physically isolates guest Wi-Fi from staff systems and staff systems from your PMS and payment infrastructure. This stops attackers who breach your guest network from reaching your critical systems. Create at least three separate networks: one for guests with no internal access, one for staff with restricted access, and one for your PMS and payment systems accessible only to authorized personnel. Implement this segmentation through managed firewalls and VLANs that enforce these boundaries automatically.
Change your Wi-Fi router’s default credentials immediately upon installation-most hotels never do, leaving attackers a direct entry point. Update your router firmware monthly and disable any guest access to device management interfaces. This simple step blocks a massive vulnerability that attackers exploit constantly.
Encrypt Data and Enforce Access Controls
Encryption protects data moving across your networks, so enforce TLS 1.2 or higher for all traffic and require multi-factor authentication for anyone accessing payment systems, the PMS, or administrative accounts. Implement role-based access controls so front desk staff can access only booking and guest information, not financial records or system configurations. A single compromised staff account should not grant access to your entire network.
Regular penetration testing reveals weaknesses before attackers find them-conduct quarterly tests specifically targeting your payment infrastructure and PMS access points. If your payment system is more than five years old, replace it rather than patch it. The cost of a new system is negligible compared to a breach that costs $3.4 million on average.
Train Staff and Test Their Response
Vulnerability assessments must happen quarterly, not annually. FreedomPay and Cornell University research found that 86% of hospitality firms cite human error as their main cybersecurity threat, and 81% lack proper employee training. This means your technical defenses fail without staff discipline. Run phishing simulations monthly and track which employees click malicious links or report suspicious emails. Staff who fail simulations require immediate retraining focused on verifying identities by calling known IT personnel directly, never sharing passwords, and recognizing social engineering tactics.
Enforce strong password policies requiring unique passwords for every system, changed quarterly, with multi-factor authentication mandatory for the PMS, payment terminals, email, and administrative access. Document your incident response plan and rehearse it twice yearly so your team knows exactly what to do when an attack occurs-who contacts guests, who notifies regulators, who isolates infected systems, and who leads recovery.
Partner With Security Experts
Partner with a managed security provider if your team lacks the expertise to monitor networks 24/7 for anomalies, patch systems consistently, and respond to threats immediately. The cost of managed services is far lower than managing breaches reactively. A provider handles continuous monitoring, applies patches on schedule, and responds to incidents before they spread across your network.
Final Thoughts
Hotel network security protects everything your hotel depends on, yet most operators treat it as optional rather than essential. A single breach costs $3.4 million on average, disrupts bookings for days, triggers regulatory fines, and destroys guest trust that takes years to rebuild. Proactive security costs far less-patching systems weekly, running phishing simulations monthly, and segmenting your networks prevents catastrophic losses while your team focuses on guest experience.
Guests increasingly check how companies handle data before booking, and strong security practices signal that their information is safe. Network segmentation, encryption, multi-factor authentication, and staff training build the trust that drives direct bookings and repeat visits-the revenue streams hospitality operators depend on for profitability. Hotels that invest in these fundamentals see immediate benefits: guests book more confidently, staff work more efficiently, and your operations run without constant fear of ransomware or payment breaches.
Start with the fundamentals today: segment your networks, enforce multi-factor authentication on critical systems, and schedule quarterly penetration tests. If your team lacks 24/7 monitoring capacity or your payment system is aging, partner with a managed security provider who handles these responsibilities. Clouddle secures hospitality operations through our Network as a Service offering, so your infrastructure stays protected while you concentrate on what matters most.