Senior living facilities hold some of the most sensitive data in healthcare. Resident medical records, financial information, and personal details make these organizations prime targets for cyberattacks.
At Clouddle, we’ve seen firsthand how a single breach can compromise hundreds of residents and damage trust instantly. This senior living cybersecurity guide walks you through the threats your facility faces and the concrete steps to defend against them.
The Real Cost of Inaction
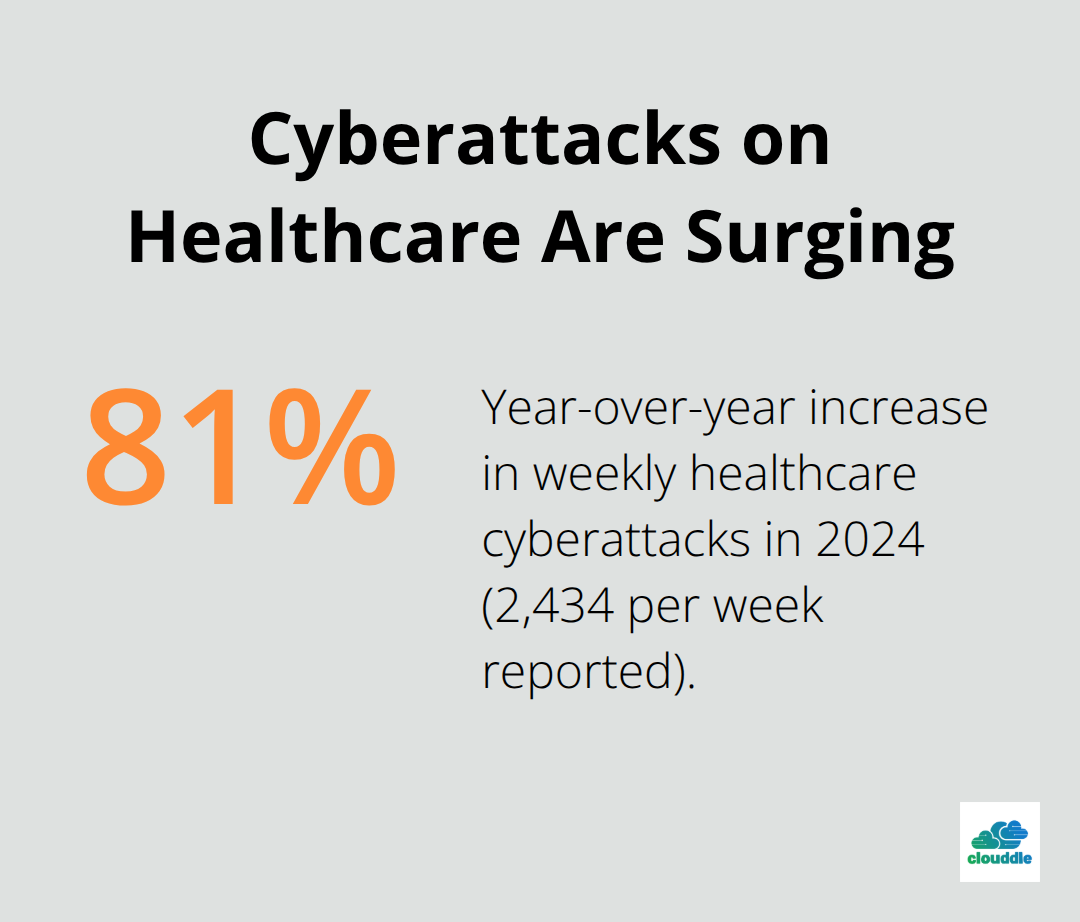
Senior living facilities face a cybersecurity crisis that extends far beyond theoretical risk. In 2024, healthcare organizations reported an average of 2,434 cyberattacks per week, an 81% increase year over year. Nursing homes and rehabilitation centers were hit particularly hard in Q1 2025, with major hacking incidents affecting more than 130,000 individuals across multiple facilities. These numbers reflect a harsh reality: senior living operators cannot afford to treat cybersecurity as a secondary concern.
The attackers targeting your facility are sophisticated and persistent. They know that senior living organizations often operate with older IT infrastructure, smaller security teams, and residents who may be less tech-savvy. Healthcare data itself is exceptionally valuable on the dark web because it contains medical histories, Social Security numbers, and financial information bundled together. Criminals understand this value and prioritize healthcare targets accordingly.
The Cascade of Damage
When a breach occurs, the damage compounds quickly. Medical record errors disrupt care, treatment delays harm residents, and operational shutdowns force staff to work manually or turn away new admissions. The financial consequences are severe-ransomware payments often exceed six figures-but the reputational damage cuts deeper. Families lose trust in your facility, occupancy rates drop, and staff morale suffers. Compliance violations add another layer of liability. HIPAA violations alone can result in penalties ranging from thousands to millions of dollars depending on breach scope and negligence.
Why Your Facility Is a Target
Your facility holds exactly what criminals want most. Seniors tend to have strong credit histories and established savings, making identity theft particularly profitable. Phone scams targeting residents generate rapid returns for minimal effort. Medical device networks connected to your systems create entry points for lateral movement once attackers gain initial access. Staff shortcuts-reusing passwords, clicking phishing links, sharing credentials-open doors that sophisticated security tools cannot close.
The threat landscape is expanding because senior living technology is expanding. Network-connected devices used by residents and operators multiply your attack surface. Many facilities still operate with immature cybersecurity programs, limited staff training, and outdated patch management. This combination creates a vulnerability gap that attackers actively exploit. The No. 1 threat remains unchanged: staff members open phishing emails and click malicious links that expose credentials to attackers. One compromised account can cascade into full system access if proper segmentation and access controls are absent.
What Compliance Actually Requires
Patient privacy laws demand more than good intentions. HIPAA requires encryption of resident data at rest and in transit. Multi-factor authentication must protect every access point to electronic health records and resident data systems.
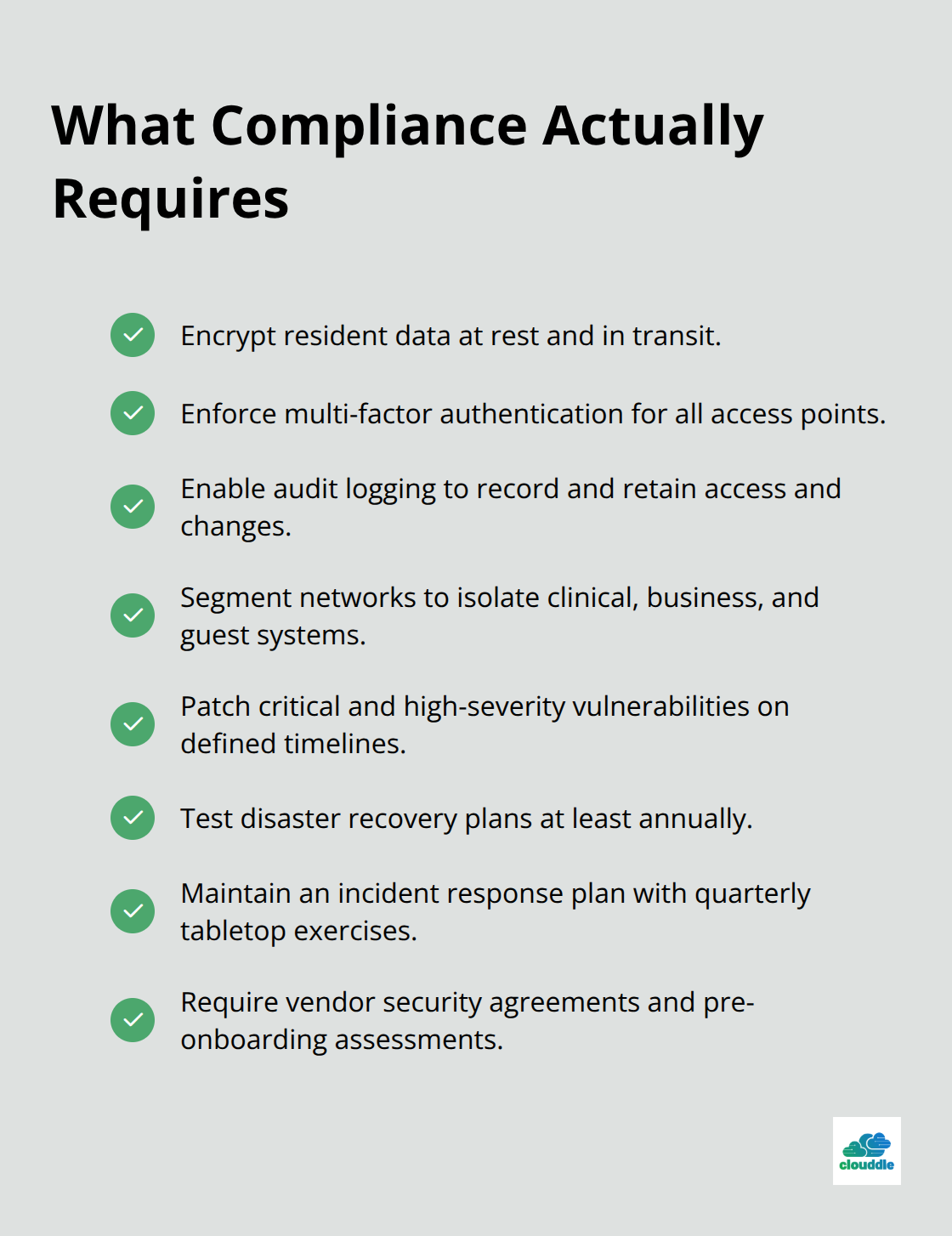
Audit logging must capture and retain detailed access records for review and investigation. Network segmentation must isolate clinical systems, business applications, and guest networks so a breach in one zone does not automatically compromise others.
Regular vulnerability assessments and patch management timelines must address critical and high-severity vulnerabilities promptly. Disaster recovery plans must be tested at least annually to confirm your facility can restore operations within acceptable timeframes after a ransomware attack or data loss event. Incident response plans must define roles, communication templates, and escalation procedures with quarterly tabletop exercises to test effectiveness. Third-party vendors handling resident data must sign security agreements with breach notification terms and undergo security assessments before onboarding.
Compliance is not a checkbox exercise. It is a framework that, when properly implemented, protects both residents and your organization from preventable harm. The specific requirements outlined above form the foundation of any credible cybersecurity program. Your next step is to assess which of these controls your facility currently has in place and which ones require immediate attention.
Common Cybersecurity Threats Senior Living Facilities Face
Ransomware has become the weapon of choice against senior living facilities because it works. Attackers encrypt medical records and operational systems, then demand payment to restore access. CISA and the FBI have flagged ransomware as a top threat to senior living, and the numbers confirm this urgency. When attackers lock down your electronic health records, residents cannot receive medications on schedule, treatment decisions stall, and staff revert to paper-based workflows that collapse under pressure. The ransom demands themselves range from tens of thousands to millions of dollars, but facilities often pay because the alternative-prolonged operational shutdown-causes immediate harm to vulnerable residents. The most dangerous aspect is that your medical devices and EHR systems connect to the same networks that handle business operations, meaning a single compromised entry point spreads laterally across your entire infrastructure if proper segmentation does not exist.
Phishing Exploits Human Behavior
Phishing remains the number one attack vector because it exploits human behavior rather than technical weaknesses. Staff members receive emails that appear to come from legitimate vendors, IT support, or even residents’ family members. The email requests password confirmation, contains a malicious attachment, or directs the user to a fake login page. One click or one credential shared, and attackers gain access to resident data systems. The sophistication of these attacks has increased significantly. Scammers now research your facility’s vendors, mimic their communication style, and time their attacks during periods when staff are rushed or distracted. They know that senior living facilities operate with limited IT staff and that front-line employees often reuse passwords across multiple systems. Once an attacker obtains credentials, they move laterally through your network, escalate privileges, and install persistent access tools before launching ransomware or exfiltrating data. Training staff to recognize phishing is essential, but training alone is insufficient. Email filtering, multi-factor authentication, and endpoint detection systems must work together to catch what human judgment misses. The reality is that even well-trained staff will occasionally click a malicious link, so your architecture must assume breach and limit the damage an attacker can inflict with a single compromised credential.
Unpatched Systems Create Permanent Doors for Attackers
Outdated systems and delayed patching represent a critical vulnerability that many senior living operators underestimate. Your facility likely runs a mix of legacy EHR systems, older medical devices, and aging network infrastructure that cannot be easily updated. Vendors stop releasing patches for older software versions, leaving known vulnerabilities unaddressed. Attackers monitor public vulnerability databases and exploit these known weaknesses because they work reliably against systems that have not been patched. CISA publishes a list of actively exploited vulnerabilities, and many senior living facilities run systems vulnerable to exploits on that list. The challenge is that patching medical devices requires coordination with vendors, testing to ensure patient safety, and scheduled downtime that disrupts operations. This creates pressure to delay updates, and delayed updates accumulate into a dangerous backlog. Firmware updates for connected medical devices, operating system patches for servers, and application updates for business software must all follow defined timelines. Critical and high-severity vulnerabilities should receive patches within 30 days of release. Many facilities miss this window because they lack formal patch management processes, inventory visibility into what systems exist, or staff capacity to execute updates. The result is that attackers find permanent doors into your network because the vulnerabilities those doors use have been publicly known for months or years.
Your facility’s attack surface expands with every connected device and every outdated system that remains in operation. The next section examines how to build defenses that actually stop these threats before they compromise resident safety and operational continuity.
How to Stop Attackers Before They Reach Your Data
Defending a senior living facility requires multiple defensive layers that work together, not in isolation. The first layer is network architecture that physically separates clinical systems, business operations, and guest networks so attackers cannot move freely once they breach one zone. NIST guidelines and CISA recommendations both emphasize that segmentation is non-negotiable. Your electronic health records system should operate on a completely isolated network segment with restricted access points. Medical devices like vital sign monitors, medication dispensers, and diagnostic equipment should have their own segmented zone with minimal connectivity to business systems. Guest Wi-Fi must be entirely separate so a visitor’s compromised device cannot reach resident data.
Implement Role-Based Access Controls
Within each segment, you implement role-based access controls where staff members access only the systems and data required for their specific job function. A receptionist should not have access to medication records. A nurse should not access billing systems. A dietary staff member should not view resident medical histories. This principle of least privilege sounds simple but requires documenting every role, mapping required access for each role, and then enforcing those restrictions through your systems. Multi-factor authentication protects every entry point to sensitive systems because credentials alone are insufficient once attackers understand how common password reuse is in healthcare. NIST standards require MFA for all staff and contractor access to electronic health records and resident data. A staff member enters their username and password, then provides a second authentication factor like a code from an authenticator app or a hardware security key. This second factor must be something the attacker does not have, even if they have stolen the password.
Audit logging captures every access to resident data, every system change, and every failed login attempt so you can review logs regularly for abnormal activity that signals an intrusion. These technical controls require ongoing management and monitoring, which is why many senior living operators lack the in-house expertise to maintain them effectively.
Train Staff to Recognize Real Threats
Staff training transforms your workforce into your strongest defensive layer, but only when training reflects actual threats your facility faces and includes practical skills staff can apply immediately. Generic cybersecurity training fails because it feels abstract and disconnected from daily work. Effective training teaches staff to recognize phishing emails with concrete examples from your industry, including emails that mimic vendor communications, family inquiries, and IT support requests. Staff should practice identifying suspicious sender addresses, unexpected attachments, and urgent language designed to bypass critical thinking.
Phishing simulations where staff receive fake malicious emails and you track who clicks malicious links reveal which staff members need additional coaching. Organizations that conduct quarterly phishing simulations see significant drops in click-through rates within six months. Your facility should also establish clear procedures for reporting suspicious activity without punishing staff who report mistakes, because fear of consequences prevents people from admitting they clicked a malicious link, which delays breach detection.
Strengthen Password and Vendor Management
Password hygiene training should emphasize that reusing passwords across systems means one compromised credential gives attackers access to multiple systems. Consider implementing a password manager so staff create unique, complex passwords without the burden of memorization. Offboarding procedures must revoke access immediately when staff depart because departing employees retain knowledge of systems and credentials that should no longer function. A formal onboarding process provisions access only to systems each new hire requires on their first day rather than granting broad access and removing it later.
Third-party vendors and contractors require the same access restrictions and monitoring as full-time staff because they represent a significant breach vector. Many facilities lack formal vendor risk management programs that assess security controls before onboarding, require security agreements with breach notification terms, and monitor ongoing compliance. Your facility should conduct tabletop exercises at least quarterly where staff walk through an incident response scenario, identify gaps in communication and procedures, and refine your playbook before an actual breach occurs.
Prepare for Ransomware Response
These exercises cost minimal resources but reveal critical weaknesses that only surface under pressure. A ransomware-specific playbook should define decision criteria for whether your facility will pay a ransom, establish coordination with local law enforcement and FBI contacts, and outline communication templates for notifying residents and families.

The combination of proper segmentation, access controls, continuous monitoring, trained staff, and tested incident response procedures creates a defense structure that stops most attacks before they compromise resident safety or operational continuity.
Final Thoughts
Protecting resident data in senior living requires commitment across your entire organization, not just from your IT department. The threats are real, the attacks accelerate, and the consequences of inaction extend far beyond financial loss. Your residents depend on you to safeguard their most sensitive information while maintaining the operational continuity that keeps their care uninterrupted.
This senior living cybersecurity guide has outlined the specific steps your facility must take: segment your networks so breaches cannot spread laterally, enforce multi-factor authentication at every access point, train staff to recognize phishing before they click, patch vulnerabilities on defined timelines, and test your incident response procedures quarterly. Facilities with mature security programs experience fewer operational disruptions, maintain resident and family trust, avoid costly compliance violations, and attract staff who feel confident their workplace takes security seriously. Your reputation depends on demonstrating that you protect resident privacy as a core operational value, not an afterthought.
Evaluate which controls your facility currently has in place and which ones require immediate attention. Prioritize network segmentation and multi-factor authentication because these controls stop the majority of attacks before they compromise resident data. If your facility lacks the in-house expertise to build and maintain these defenses, Clouddle provides managed IT, networking, and security services specifically designed for senior living operators.



0 Comments