At its core, access control is all about managing who can go where and when. It’s the gatekeeper for your property, deciding who gets a key, which doors that key can open, and even the times it will work. The three main models for this are Discretionary (DAC), Mandatory (MAC), and Role-Based (RBAC).
These models are the rulebooks that determine who can access your most important physical and digital assets. Getting a handle on them is the first step to building a security system that actually works for your property.
To give you a quick overview, here's a high-level summary of the three main logical access control models. This table outlines their core principles and typical use cases to get you started.
Quick Comparison of Access Control Models
| Model | Core Principle | Best For |
|---|---|---|
| Discretionary (DAC) | The resource owner decides who gets access. Very flexible. | Small teams, startups, and environments where flexibility is key. |
| Mandatory (MAC) | Access is determined by a central authority based on security levels (e.g., "Top Secret"). | Government, military, and high-security data centers. |
| Role-Based (RBAC) | Permissions are assigned based on a person's job title or function (e.g., "Manager," "Tenant"). | Most businesses, multi-family properties, and commercial buildings. |
As you can see, the right model really depends on your specific security needs and how your organization operates. We'll dive deeper into each of these throughout this guide.
Why Access Control Is Your Digital and Physical Gatekeeper

Think of it this way: in a modern building, that "key" might be a physical key card, an app on your smartphone, or even your fingerprint. Access control is the brain behind the lock, making the decisions.
For property owners and IT managers, this gatekeeper role has become absolutely essential. We're not just talking about keeping doors locked anymore. It’s about safeguarding assets, protecting people, and making daily operations run smoother. A weak system is a welcome mat for security breaches, but a well-designed one is a powerful, almost invisible, part of your building's success.
The Two Sides of Security
At its heart, every access control system runs on one simple but powerful idea: give the right people the right level of access, at just the right time. This isn't just for physical doors; it applies to your digital world, too.
Physical Access Control: This is what most people think of first. It’s about managing who can get into tangible spaces like your main entrance, specific floors, server rooms, or individual apartment units.
Logical Access Control: This side of the coin controls access to your digital assets. Think company networks, sensitive financial files, resident databases, or specific software platforms.
For true security, these two have to be in sync. A high-tech lock on the front door means nothing if your company's most sensitive data is open for any employee to see. Likewise, strong passwords won't help much if an unauthorized person can just wander into the server room and unplug the hardware.
An effective security strategy weaves both physical and logical access controls together. This creates layers of protection, ensuring that only authorized people can enter a restricted area and access the sensitive data stored within it.
Why Choosing the Right Model Matters
Picking an access control model isn't just a technical choice; it's a fundamental business decision with lasting impact. The approach you select will directly influence how permissions are managed, how easily your system can grow with you, and the actual level of security it provides.
For example, a small, creative agency might do just fine with a flexible system where team leads can grant access to project folders on the fly. On the other hand, a commercial building that houses a financial firm and a healthcare clinic needs a much stricter, centrally managed system where permissions are non-negotiable and based on defined roles.
Understanding the different types of access control for business is the first real step toward building a security framework that is both strong and sensible. As we explore the main models, you'll see exactly how each one fits different operational needs, security risks, and business goals.
Understanding the Three Core Models of Access Control
Before you can pick the right lock, you need to understand the logic behind it. At their core, all access control systems run on a set of rules that decide who gets a key and who doesn’t. Think of them as different philosophies for managing permissions.
While there are countless variations out there, almost every system you’ll encounter is built on one of three foundational models. Getting a handle on these three—RBAC, DAC, and MAC—is the first real step to designing a security framework that actually works for your property.
Role-Based Access Control (RBAC): The Organized Approach
There’s a reason Role-Based Access Control, or RBAC, is the most popular model on the market. It’s built on a beautifully simple and scalable idea: you don’t grant access to people, you grant it to roles.
Think about how a large hotel or multi-family community operates. Instead of creating a custom set of permissions for every single staff member, you create roles like "Front Desk," "Maintenance," or "Property Manager." Each role has its access rights already baked in.
- Maintenance: Can access utility closets and vacant units during business hours, but not occupied apartments or the main office.
- Front Desk: Can access the reservation system and common areas like the lobby and gym, but not staff-only back offices.
- Property Manager: Has broad access to most areas, including financial systems and all residential units for emergencies.
When a new person joins the maintenance team, you just assign them the "Maintenance" role. Instantly, they have all the permissions they need—and none they don’t. If they switch to a front desk position, you just swap their role. It’s efficient, clean, and dramatically reduces the chance of human error.
This scalability is why RBAC dominates the industry. In fact, it holds a massive 48% market share as of 2024. The global access control market, which leans heavily on RBAC, is on track to grow from USD 12.01 billion in 2025 to an estimated USD 25.15 billion by 2034. You can see the complete breakdown in this access control market growth report from Precedence Research.
Discretionary Access Control (DAC): The Owner-Driven Approach
Next up is Discretionary Access Control, or DAC, which flips the script and puts the power right in the hands of the resource owner. The best parallel here is sharing a Google Doc. The person who created the file (the "owner") has total discretion to decide who can view, edit, or comment on it.
In a DAC system, every access point—a digital file, a specific office, or a smart lock on an apartment door—has an owner. That owner is responsible for maintaining an Access Control List (ACL), which is just a simple list of who’s allowed in and what they’re allowed to do.
Key Takeaway: With DAC, control is spread out. Individual owners make the calls for the resources they manage, which offers incredible flexibility for dynamic situations.
For example, a property manager could grant a plumber one-time access to a specific unit’s smart lock for a two-hour window. The manager "owns" that door’s access and can give the plumber temporary credentials without needing to loop in a central administrator. The trade-off, however, is that this model can become a security headache in larger organizations, since it relies entirely on individuals to manage permissions correctly and consistently.
Mandatory Access Control (MAC): The Top-Down Approach
Finally, there’s Mandatory Access Control, or MAC. This is the strictest, most rigid model of the three, and for good reason. Access isn’t determined by a person's role or an owner's choice; it’s dictated by a central authority that assigns security labels to everything and everyone.
The classic analogy for MAC is a high-security government or military environment.
- People get a clearance level: For instance, "Confidential," "Secret," or "Top Secret."
- Resources get a classification level: A specific folder might be labeled "Secret."
The system then enforces one simple, unbreakable rule: you can only access something if your clearance is equal to or higher than its classification. Someone with "Secret" clearance can view "Secret" and "Confidential" files, but they’ll be blocked from a "Top Secret" file every single time.
With MAC, individuals have zero say in permissions. You can't share access to a file you're working on, even if you created it. The rules are mandatory and hard-coded into the system. This ironclad structure makes MAC the go-to for organizations where preventing data leaks is the number one priority.
While these are the core models, they are often combined and adapted. You can learn more about how they are applied in our guide to the broader categories of access control systems.
Comparing the Pros and Cons of Each Access Control Model
Knowing the theory behind different access control models is one thing, but actually choosing the right one for your property is a completely different challenge. The best fit always comes down to a careful balancing act between your security needs, day-to-day operational flexibility, and the administrative effort you can afford.
Each model—MAC, DAC, and RBAC—comes with its own distinct set of trade-offs. To make the right call, you need to look at them through the lens of what really drives your business: how tight does security need to be, how easy is the system to manage, and can it grow with you?
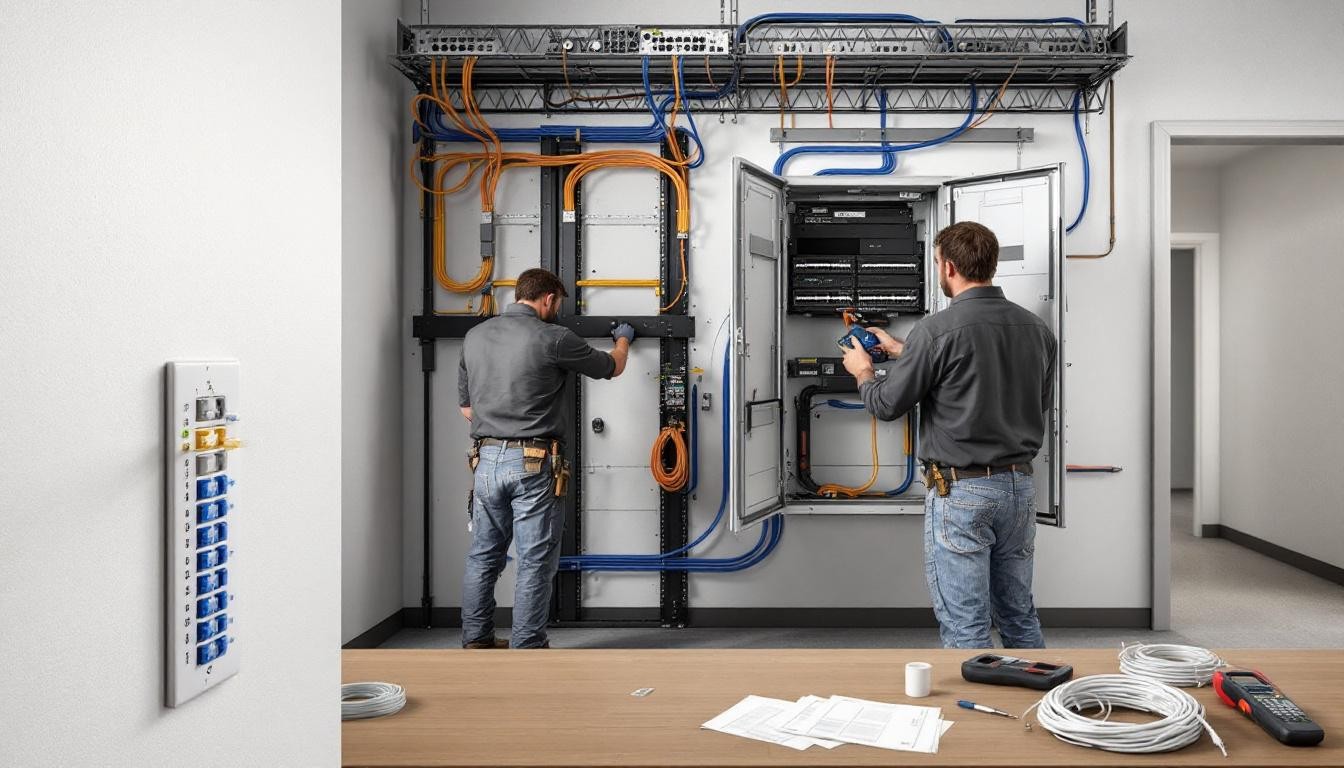
This diagram breaks down the core idea behind each of the three main logical access control models.

You can see the clear difference: RBAC is all about job functions, DAC centers on individual ownership, and MAC is built around strict, centralized security labels.
Mandatory Access Control (MAC): The Fortress
When you need absolute, uncompromising security, Mandatory Access Control is the only real option. Think of it as a fortress. Its rigid, top-down structure is designed to make unauthorized access or data leaks virtually impossible.
The Good: It delivers the highest level of security you can get. The system enforces all the rules automatically based on security clearances, which takes human error out of the equation. This makes it perfect for environments handling classified information, like government agencies or military contractors.
The Bad: That rigidity is also its biggest drawback. MAC is terribly inflexible and complex to manage. It’s a poor fit for dynamic businesses like a hotel or apartment building where access needs are constantly in flux. The administrative burden of classifying every single user and resource is immense.
Honestly, this level of security is a feature, not a bug, but it makes MAC completely impractical for most commercial properties. You wouldn't use a fortress to guard the community pool.
Discretionary Access Control (DAC): The Flexible Collaborator
At the complete opposite end of the spectrum is Discretionary Access Control. DAC is all about flexibility. It empowers the "owner" of a resource—like a file, a room, or a piece of equipment—to decide who gets access. It’s like giving your team leads the keys and trusting them to hand out copies as they see fit.
While RBAC is a popular choice, DAC holds a strong position, particularly in markets where physical hardware is central. For instance, Discretionary Access Control (DAC) is a key component in the hardware-focused segment of the market, which is projected to command a 58.2% market share by 2026. This is because physical readers and on-site controllers let property owners set the rules directly. In hospitality, this on-the-fly flexibility is a lifesaver for handling last-minute vendor access or special guest requests. You can dive deeper into these trends in the complete Future Market Insights report on the access control market.
The Good: DAC is incredibly flexible and easy for end-users to manage. It allows for quick permission changes without waiting for a central administrator, which is great for small teams or properties with constantly shifting needs.
The Bad: Its greatest strength is also its biggest weakness. With security decisions decentralized, you can end up with inconsistent rules and glaring security gaps. As an organization gets bigger, just trying to track who has access to what becomes a messy, high-risk nightmare.
Role-Based Access Control (RBAC): The Balanced Scaler
For most businesses, Role-Based Access Control is the perfect middle ground. It strikes a practical balance between the ironclad security of MAC and the freewheeling nature of DAC. By linking permissions directly to a person's job function or role, RBAC creates a system that’s structured and predictable without feeling suffocating.
At its heart, RBAC is all about the principle of "least privilege." People get exactly the access they need to do their job—and nothing more. This one concept dramatically simplifies administration while shrinking your potential attack surface.
This model is a natural fit for structured organizations like commercial office buildings, multi-family communities, senior living facilities, and hotels.
The Good: RBAC is incredibly scalable and simple to manage as your organization grows. Bringing on a new team member or handling a departure is as easy as assigning or removing a role. This also makes security audits much cleaner and ensures policies are applied consistently everywhere.
The Bad: The initial setup requires some real thought. You have to carefully map out all the different roles in your organization and define what permissions each one needs. For a very small or chaotic company, the structure of RBAC might feel like overkill compared to the simple ownership model of DAC.
Feature Showdown: RBAC vs. DAC vs. MAC
To see how these models stack up head-to-head, it helps to put their core attributes side-by-side. This table compares them across the features that matter most when you're making a decision.
| Feature | Role-Based (RBAC) | Discretionary (DAC) | Mandatory (MAC) |
|---|---|---|---|
| Primary Logic | Permissions are assigned to job roles, not individuals. | Resource owners grant or deny access to other users. | System enforces access based on security labels and clearances. |
| Flexibility | Moderate. Easy to change a user's role. | High. Owners can change permissions at any time. | Low. Extremely rigid and centrally controlled. |
| Security Level | High. Enforces "least privilege" and prevents privilege creep. | Low to Moderate. Prone to human error and inconsistencies. | Very High. The most secure model available. |
| Scalability | Excellent. Manages thousands of users with ease. | Poor. Becomes unmanageable and insecure at scale. | Good. Can scale, but with immense administrative overhead. |
| Admin Effort | Low (after setup). Manage roles, not individuals. | Low (initially). Becomes high as complexity grows. | Very High. Requires constant classification and management. |
| Best For | Most businesses, hospitality, commercial, senior living. | Small teams, startups, collaborative projects. | Government, military, high-security research facilities. |
As you can see, there's no single "best" model—only the best model for a specific context. The trade-offs are clear: MAC prioritizes security above all else, DAC prioritizes flexibility, and RBAC offers a scalable balance of both.
Ultimately, picking the right access control model comes down to a clear-eyed assessment of your property’s unique risks, operational workflows, and future growth plans. While MAC and DAC certainly have their niche uses, RBAC’s powerful blend of security, scalability, and streamlined management makes it the go-to choice for the vast majority of modern properties.
Seeing Access Control in Action Across Different Industries

Theory is one thing, but seeing the different types of access control work in the real world is where it all clicks. The best model—or often, a blend of models—really depends on the unique challenges of a specific property. It’s all about finding the right fit for security, daily operations, and the people using the space.
Let’s look at how these systems solve real problems in hospitality, multi‑family housing, and commercial properties. These aren't just security features; when done right, they become a core part of the business.
Hospitality: A Masterclass in Role-Based Control
Hotels are the perfect, living example of Role-Based Access Control (RBAC). Think about it: you have a constant flow of guests, vendors, and a diverse staff, all needing different levels of access. Trying to manage permissions for each person individually would be an absolute nightmare.
Instead, hotels use RBAC to bring order to that chaos.
- The Challenge: How do you give hundreds of staff members access only to the areas they need for their job, while also making sure a guest’s key works for their room but nowhere else, and only for the duration of their stay?
- The Answer: A modern RBAC system ties permissions to pre-defined roles like "Housekeeping," "Front Desk," or "Guest."
- The Result: A housekeeper’s keycard opens guest rooms on their assigned floor but gets denied at the manager's office. Front desk staff can get into the back office but not the maintenance closets. A guest's key simply stops working after checkout.
By assigning permissions to roles instead of people, a hotel can instantly update or revoke access when an employee's job changes or they leave the company. This move alone dramatically cuts down on security risks and makes day-to-day operations run so much smoother for everyone.
Multi-Family Living: Blending DAC with Modern Tech
Apartment and condo buildings face a different puzzle. Residents need ironclad, reliable access to their own homes and shared amenities like a gym or pool. At the same time, they want the flexibility to grant temporary access to others—think dog walkers, cleaners, or package deliveries.
This is where a modern system shines, often mixing the flexibility of Discretionary Access Control (DAC) with the convenience of mobile technology.
- The Challenge: A resident is at work but needs to let a delivery driver into the lobby to drop a package in a secure locker.
- The Answer: The building has a smart intercom system connected to a mobile app. The resident gets a video call on their phone from the delivery person, verifies who they are, and taps a button to unlock the lobby door remotely. They can even issue a one-time digital key for the package room.
- The Result: The delivery is made securely without the resident ever leaving their office. This DAC-style approach gives residents the control they want, adds a layer of convenience, and frees up property managers from having to handle every single entry.
It’s the best of both worlds: residents feel empowered, and the building's main perimeter stays secure.
Commercial Properties: Integrating for Total Security
Commercial office buildings often have multiple tenants under one roof, each with its own security needs. They also contain high-value areas like server rooms that need fortress-like protection. For these properties, an integrated system that combines RBAC with strong physical controls is non-negotiable.
For example, many buildings use tough commercial physical access solutions like gates and turnstiles to create a secure perimeter. These physical barriers then work in concert with the digital access rules.
An employee might swipe their badge to get through the main lobby turnstile, but that same badge won't get them onto another company's floor. Their access is defined by their role within their specific organization.
- The Challenge: A multi-tenant office building needs to secure its main entrances, individual tenant suites, and critical infrastructure like IT closets.
- The Answer: A unified access control system is deployed. It uses RBAC to assign permissions based on a person’s company and job title. Access to the server room, for example, is limited to a small handful of senior IT staff.
- The Result: Security becomes granular and layered. A marketing associate can get to their own office floor during business hours, but their badge is denied at the server room door 24/7. This integrated setup shows how different types of access control can work together to let people move efficiently where they belong while keeping sensitive areas locked down tight.
How to Implement or Modernize Your Access Control

Knowing the different models of access control is one thing; putting that knowledge into practice is where you truly start to secure your property. Whether you're building a system from scratch or overhauling an outdated one, think of it as a clear-headed project, not a one-off task. The goal is to figure out what you have, define what you actually need, and then pick the right tools for the job.
This isn't just about choosing a new type of lock. It's about creating a complete security environment that protects your people and assets today, while also being flexible enough for whatever comes next.
Conduct a Thorough Security Audit
You can't build a better system until you know exactly where the current one is failing. A security audit is your ground zero—a top-to-bottom review of every physical and digital access point. Think of it as drawing a detailed map of your property's defenses before you decide where to place your guards.
This audit needs to answer a few critical questions:
- Who has access right now? Make a list of every single person, their role, and the permissions they currently hold. You might be surprised by what you find.
- Where are the weak points? Pinpoint every unsecured door, shared PIN code, or server closet that anyone can walk into.
- What are your biggest risks? Is it a former tenant still having access, theft from a commercial unit, or a data breach from an unsecured network room?
The whole point is to get an honest look at your vulnerabilities. This audit will become the blueprint for every decision that follows, making sure your new system solves your real-world security problems.
Choose the Right Hardware and Software
Once your audit is done, you can start shopping for the actual components. This is always a balancing act between tough security, ease of use for tenants or employees, and the long-term cost of ownership.
Hardware Selection:
The hardware pieces are what people will interact with every day, so they need to be tough, dependable, and right for the environment.
- Card Readers: These are the workhorses of access control. They're proven, reliable, and a great fit for main entrances and common area doors.
- Keypad Entry: Good for convenience, but security can be a concern if codes get passed around. Best used in lower-risk areas.
- Biometric Scanners: For your most sensitive areas, like data centers or equipment rooms, biometrics offer top-tier security with fingerprint or facial scans.
- Smart Locks: A game-changer for multi-family and hospitality properties. They offer mobile key access and can be managed from anywhere.
Software and Management:
Your software is the system's brain. More and more properties are ditching clunky on-site servers and moving to the cloud. Cloud-managed systems are simply easier to run—they allow for remote updates, monitoring from anywhere, and cut out the expense of maintaining server hardware. This also makes it far easier to connect with other smart building technologies.
A modern security principle that works hand-in-glove with access control is the Zero Trust model. The rule is simple: never trust, always verify. This means every single access attempt is challenged and authenticated, no matter if it’s coming from inside or outside your property. It’s a mindset that dramatically strengthens any access control system you choose.
Upgrading from a Legacy System
If you're replacing an old, clunky system, the migration requires careful planning to avoid creating security gaps or frustrating everyone. Following Role Based Access Control best practices is a great starting point for structuring your new permissions logically.
Here’s a simple checklist to guide you through a smooth upgrade:
- Define Your Roles (RBAC): Before you even order hardware, figure out who needs access to what. Create roles like "Resident," "Maintenance Staff," or "IT Admin" and map out their specific permissions.
- Phase Your Rollout: Don't rip and replace everything at once. Start with a single floor or a low-traffic building to test the new system and iron out any issues.
- Train Your People: A new system is worthless if no one knows how to use it. Run quick training sessions for your staff and send out clear, simple instructions for residents on using their new credentials.
- Run Systems in Parallel: For a short transition period, keep both the old and new systems running. This gives people time to adjust and ensures no one gets locked out.
- Decommission the Old System: Once you're confident the new system is stable and everyone is comfortable, it's time to pull the plug. Fully deactivate and remove the old hardware to eliminate any lingering security holes.
A little planning goes a long way. For an even more detailed walkthrough, check out our guide on access control system installation to ensure a successful deployment from start to finish.
Answering Your Top Access Control Questions
When you start digging into modern security systems, a few big questions always surface. It’s a field full of technical jargon and different options, and getting straight answers is the only way to feel good about your decision. Let’s tackle the questions we hear most often from property managers and business owners.
We'll clear up the basics and show you what a modern, managed approach to security actually looks like on the ground.
Physical Versus Logical Access Control
One of the first things to get straight is the difference between "physical" and "logical" access control. They might sound similar, but they protect two completely different parts of your operation. The easiest way to think about it is one controls the real world, and the other controls the digital world.
Physical access control is exactly what it sounds like—it manages who can go where. Think doors, gates, and elevators. It’s the system that lets a resident into the gym with a fob or stops a stranger from wandering into a server room. The tools are things you can touch: key cards, electronic locks, and biometric scanners.
Logical access control is all about your data and networks. It’s what stops an employee from seeing sensitive financial files or prevents a resident from accessing another tenant's account information. This is handled with passwords, multi-factor authentication (MFA), and specific user permissions set up in your software.
You absolutely need both. A strong lock on the server room door (physical) is useless if any employee can log in and view confidential data from their desk (logical). A complete security strategy makes sure both your physical spaces and digital assets are properly locked down.
The Real Cost of a Modern Access Control System
For a long time, upgrading security meant writing a huge check for hardware and installation. That massive upfront cost put the best technology out of reach for many properties. Thankfully, that model is becoming a thing of the past.
The entire industry is shifting toward Access Control as a Service (ACaaS).
Instead of a painful capital expense, ACaaS turns security into a predictable subscription. You pay a simple monthly or annual fee that wraps everything together—the hardware, software, professional installation, ongoing maintenance, and even 24/7 support.
This approach does more than just make top-tier security affordable. It keeps your system current. As technology evolves, your provider handles all the updates and upgrades. You get the latest security features without ever having to face another massive bill, turning a potential budget-breaker into a manageable operating expense.
Integrating New Systems with Existing Cameras
"I already have security cameras. Will a new access system work with them?" This is a perfectly valid concern, especially if you've already invested heavily in video surveillance. The great news is that modern, IP-based access control platforms are designed to play nicely with other systems. The era of siloed security tools that can't communicate is over.
When you connect your access control with your video management system (VMS), you’re not just linking them; you’re creating a single, much smarter security hub. This integration makes a real difference in your day-to-day operations.
- See the Full Story: When someone uses a credential at a door, that event is automatically tied to the video footage from the nearest camera for that exact moment.
- Find What You Need, Fast: Got an alert for a "forced door"? Instead of hunting through hours of footage, you can just click the alert and instantly watch the video of the incident.
- Verify in Real-Time: You can see who is swiping a card and immediately confirm it’s the right person, adding a crucial layer of visual verification.
This seamless connection gives you a much clearer picture of what's happening on your property and cuts down investigation time from hours to minutes.
Ready to modernize your property's security with a system that's both powerful and affordable? Clouddle Inc offers fully managed access control solutions with zero upfront costs, flexible terms, and 24/7 support. Learn how Clouddle can integrate your security and boost your operational efficiency today.