Hotels managing multiple properties face a fragmented security nightmare. Legacy systems don’t talk to each other, creating blind spots that put guests and staff at risk while draining budgets through redundant tools and manual oversight.
Unified security for hotels solves this. At Clouddle, we’ve seen firsthand how centralized protection transforms operations-reducing response times, cutting costs, and giving managers real visibility across every location.
Why Hotels Need Unified Security Management
The global hotel security market reached USD 10.87 billion in 2024 and is projected to hit USD 22.61 billion by 2033, according to DataIntelo’s Hotel Security Market Report. This explosive growth reflects a hard reality: hotels face rising security threats, and fragmented systems cannot keep pace. Room break-ins, vehicle theft, unauthorized access to guest floors, and data breaches inflict operational damage that chains managing dozens or hundreds of locations cannot absorb easily. Properties without centralized monitoring suffer delayed threat detection-security teams respond minutes or hours after incidents occur.

That delay costs money, damages guest trust, and triggers liability claims that multiply across a portfolio.
Security Threats Accelerate in Open Environments
Hotels operate as open environments where thousands of unfamiliar people pass through daily. This openness drives business but creates multiple attack vectors that traditional, disconnected security systems miss entirely. When surveillance cameras operate independently from access control systems, and alarms fail to communicate with video feeds, security teams lack the integrated visibility needed to identify suspicious patterns. A guest using a cloned keycard at 3 AM might trigger an alarm in one system while cameras in another system record footage that nobody watches. Luxury properties now adopt biometric access controls, AI-powered surveillance, and integrated threat detection to address this fragmentation, but mid-market and budget hotels often lack resources to operate multiple disconnected systems effectively. The result is reactive security rather than proactive protection-teams respond to incidents instead of preventing them.
Fragmented Systems Drain Resources Across Properties
A regional hotel chain with ten properties typically operates ten separate security ecosystems: ten different camera systems, ten different access control platforms, ten different alarm providers. This fragmentation prevents security managers from viewing live feeds from all locations on a single dashboard. Real-time alerts across properties become impossible, and incident response coordination requires manual phone calls and email chains. Cloud-based centralized management enables real-time monitoring and control across entire portfolios, improving response times dramatically. Without it, a security incident at property seven goes unnoticed while the on-site team handles an unrelated issue at property four. Staffing compounds this problem-hotels must maintain dedicated security personnel at each location or contract with multiple managed security service providers, each operating independently. The operational overhead becomes staggering, and consistency across properties evaporates.
Inconsistent Protocols Create Blind Spots
Each location enforces slightly different protocols, uses different tools, and maintains different audit trails, making it nearly impossible for corporate leadership to understand actual security posture across the portfolio. One property might use mobile credentials while another relies on physical keycards. One location responds to alarms within minutes while another takes hours. These inconsistencies create gaps that bad actors exploit. A thief familiar with one property’s security gaps can apply that knowledge to another location in the same chain. Data breaches at one location compromise guest information across the entire portfolio if systems don’t communicate. Compliance becomes a nightmare-auditors struggle to verify that all properties meet regulatory requirements when each location maintains separate records and procedures. This fragmentation also prevents hotels from identifying patterns that span multiple properties. A coordinated theft ring operating across three locations might go undetected because each property’s security team works in isolation.
Unified Systems Enable Consistent Protection
Centralized security platforms eliminate these blind spots. Real-time alerts across properties enable faster incident response and coordinated actions to protect guests and assets. Cloud-based, multi-site management reduces the need for on-site monitoring staff, cutting labor costs across hotel chains. Centralization ensures consistent security standards and uniform protocols across every property. Remote access to security feeds allows managers to monitor security from anywhere, improving oversight across regions. Scalable architecture supports adding new hotels without reengineering the entire system. Data analytics from centralized monitoring identify patterns and hotspots (high-risk zones, for example) to optimize resource allocation. These capabilities transform how hotels protect their operations-but only if the right platform integrates access control, surveillance, alarms, and monitoring into one cohesive system.
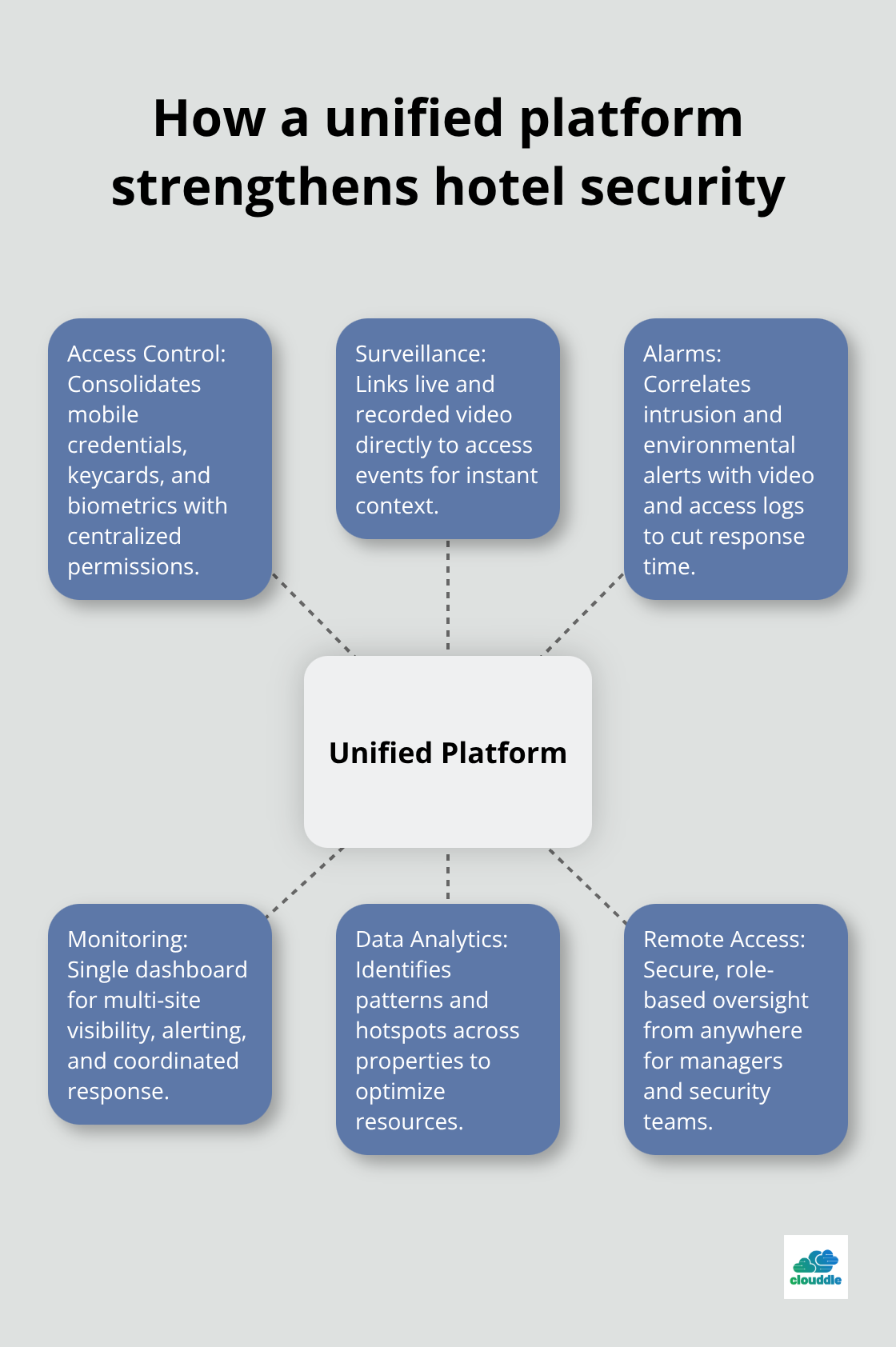
Building a Unified Security Infrastructure
Connect Access Control and Surveillance Systems
Integrating access control and surveillance into one platform eliminates the communication gaps that plague fragmented systems. Hotels need to connect electronic keycard systems, mobile credentials, and biometric readers directly to video management software so that when a cloned card triggers an access event, cameras automatically record footage from that specific entrance and timestamp it precisely. This integration works only when vendors provide open APIs and smart middleware that bridge legacy systems with modern platforms without forcing hotels to rip-and-replace existing hardware. A regional hotel chain operating older surveillance infrastructure can connect those cameras to a new centralized access control platform through middleware adapters, preserving existing camera investments while gaining unified visibility. The alternative-replacing every camera, every access control reader, and every alarm panel across ten properties simultaneously-costs hundreds of thousands of dollars and creates months of operational disruption.
When access control and surveillance communicate, security teams spot coordinated threats instantly. A guest using a stolen keycard at 2 AM triggers an alert that pulls live video from four angles, enabling staff to respond before the guest reaches the target room. Without integration, that keycard swipe creates a log entry somewhere, and video from a different system records footage that nobody watches in real time.
Monitor All Properties from a Single Dashboard
Real-time monitoring across properties demands a single dashboard where security personnel view live feeds from all locations, receive instant alerts, and dispatch responses without manual coordination. Cloud-based centralized management reduces the need for dedicated on-site security staff at each property; one team of three monitors ten properties instead of ten properties each maintaining their own guard. Hotels using this approach report dramatically faster incident detection and response-threats that once took 30 minutes to identify now surface within seconds.
Centralized video monitoring lets security teams view live feeds from all hotel locations on one dashboard for real-time oversight. Remote access to security feeds allows managers to monitor security from anywhere, improving oversight across regions. This visibility transforms how hotels respond to threats across their entire portfolio.
Automate Incident Response Protocols
Streamlined incident response depends on clear protocols that every property follows identically. When an alarm triggers at property seven, the system automatically records video, logs access events, alerts the nearest staff member, and notifies the central security team-no phone calls, no delays, no confusion about which property needs help. Integration with Property Management Systems means the system knows which guest occupies which room, enabling security teams to cross-reference access logs with reservation data to distinguish authorized from unauthorized entry.
A guest entering room 412 using their assigned mobile credential shows as expected; an unauthorized person using a cloned card shows as a threat. This layered approach transforms security from reactive incident response into proactive threat prevention across the entire portfolio. Consistent protocols across all locations ensure that every property responds to threats the same way, eliminating the gaps that bad actors exploit.
Leverage Data Analytics to Optimize Security
Data analytics from centralized monitoring identify patterns and hotspots (high-risk zones, for example) to optimize resource allocation. Security teams can analyze access logs, video footage, and alarm data across all properties to spot coordinated theft rings or systematic vulnerabilities that span multiple locations. These insights allow hotels to shift security resources to areas where threats actually occur rather than spreading staff thin across every entrance.
Scalable architecture supports adding new hotels without reengineering the entire system. As hotel chains expand, new properties connect to the same centralized platform, inheriting the same protocols, the same visibility, and the same level of protection from day one. This foundation positions hotels to address the next critical challenge: protecting guest data and staff credentials within the unified security ecosystem.
What Security Features Actually Protect Hotels
Protect Guest Data and Payment Information
Guest data protection ranks as the most critical security feature because a single breach exposes thousands of room numbers, credit card details, and personal information that compromise your entire portfolio’s reputation. Hotels processing payment card data must comply with PCI DSS standards, meaning your unified security platform needs end-to-end encryption, multi-factor authentication, and continuous monitoring to prevent unauthorized access to payment systems and guest records. Many hotels treat cybersecurity as separate from physical security, but a stolen keycard grants access to rooms while a compromised PMS database grants access to guest payment methods and reservation histories simultaneously. Your unified platform must integrate physical access logs with network monitoring so that when someone uses a cloned card at 2 AM, your security team sees both the access event and any suspicious data traffic from that location happening in real time. This dual visibility prevents thieves from exploiting the gap between physical intrusion and digital data theft.
Create Accountability Through Staff Access Logs
Staff access management creates accountability through detailed audit trails that show exactly who accessed which areas at what times, making investigations faster and reducing liability when incidents occur. A housekeeping employee swiping into a guest room generates a timestamp, location record, and camera footage linked to their mobile credential, creating an irrefutable record that protects both guests and staff from false accusations. Integration with your Property Management System transforms fragmented security data into actionable intelligence by connecting access control directly to reservation systems so that unauthorized entries trigger alerts only when they occur outside expected check-in windows. A guest arriving at 11 PM using their assigned mobile credential shows as normal; that same room accessed at 3 AM by an unknown credential shows as a threat requiring immediate investigation. This context-aware alerting reduces false positives that plague traditional systems and prevents alert fatigue from overwhelming your security team.
Combine Access Control, Surveillance, and Alarms Into One System
The strongest hotel security ecosystems combine access control, surveillance, alarms, and monitoring into one cohesive platform where these systems operate as integrated tools rather than isolated components. Hotels that separate these functions waste resources on redundant hardware, duplicate alert processing, and staff coordination overhead that slows response times to seconds or minutes when they should respond in milliseconds. Your unified platform should provide role-based dashboards so that property managers see occupancy and security summaries, engineers access live equipment status, and security teams get detailed forensic data for investigations without forcing everyone through the same interface.
Track Metrics and Identify High-Risk Zones
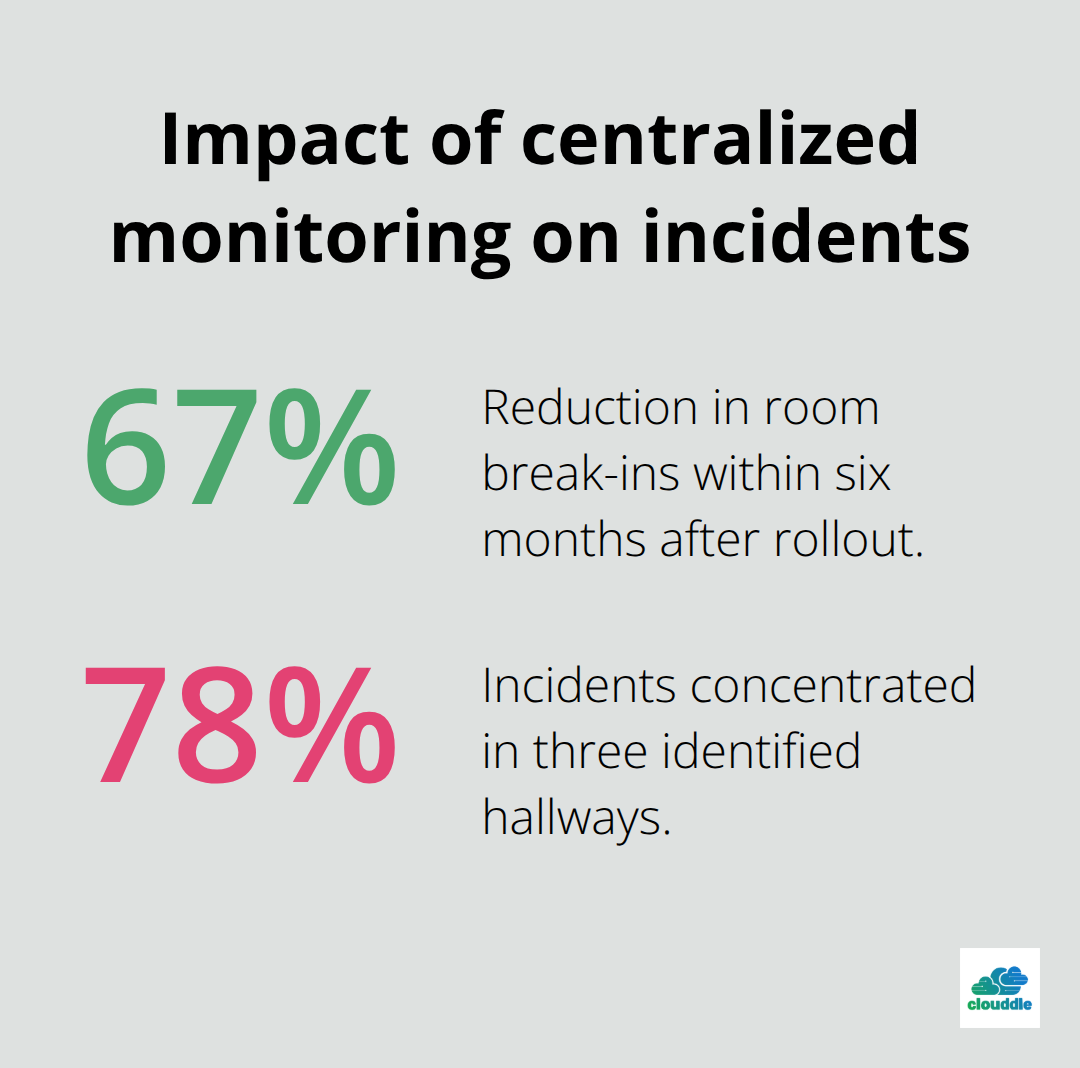
Real-time analytics dashboards turn operational data into measurable security improvements by tracking metrics like unauthorized access attempts, average incident response times, and high-risk zones where theft concentrates. One regional hotel chain operating fifteen properties reduced room break-ins by 67 percent within six months after implementing centralized monitoring because their security team identified that three specific hallways on lower floors accounted for 78 percent of incidents, allowing them to deploy visible cameras and staff presence where threats actually occurred rather than spreading resources evenly across all entrances. Compliance becomes straightforward when your platform automatically generates audit trails, maintains detailed access logs, and provides evidence for investigations without manual record-keeping across multiple disconnected systems.
GDPR compliance requires data protection by design, meaning your security platform must process guest data only when necessary for legitimate security purposes and delete recorded footage within defined retention periods automatically rather than relying on manual processes that fail consistently.
Final Thoughts
Unified security for hotels eliminates the operational chaos that fragmented systems create. When access control, surveillance, alarms, and monitoring operate as separate tools, hotels waste money on redundant infrastructure, lose visibility across properties, and respond to threats too slowly to prevent damage. Centralized platforms change this equation entirely-security teams monitor all locations from one dashboard, respond to incidents in seconds instead of minutes, and identify patterns that span multiple properties before they escalate into coordinated theft rings or systematic vulnerabilities.
The financial case proves equally compelling. Cloud-based centralized management reduces the need for dedicated security staff at each property, cutting labor costs dramatically across hotel chains. One team of three monitors ten properties instead of ten properties each maintaining their own guard, while AI-powered analytics reduce false alerts by over 90 percent compared to traditional systems, improving alert quality and preventing staff fatigue. Hotels eliminate duplicate hardware purchases, consolidate vendor relationships, and reduce maintenance overhead by operating unified systems rather than managing ten separate ecosystems.
Consistency across locations transforms how hotels protect guests and staff, and uniform protocols ensure that every property responds to threats identically. At Clouddle, we understand that unified security requires reliable networking infrastructure, managed IT support, and security services working together seamlessly-Clouddle’s Network as a Service bundles connectivity, security, and support without requiring upfront capital investment, allowing hotels to implement unified security across their entire portfolio without the financial burden of traditional deployments.



0 Comments